
ICYMI in March: here’s what happened in G Suite
Just like that, another month down.
In March, we announced a slew of security updates to Google Cloud, including enhancements to G Suite. In a nutshell, G Suite companies can now use advanced configurations to help fend off phishing scams.
These updates will continue to help businesses block (ph)ishy activity, like if an untrusted sender tries to share encrypted attachments or if someone tries to trick you by sending information from a domain that looks like yours.
With these protections in place, more than 99.9 percent of Business Email Compromise (BEC) scenarios—when someone impersonates an executive to get sensitive information—are automatically moved to spam or flagged to users as shifty. Sorry, Charlie.
We also automatically enabled basic device management for mobile devices that access G Suite. Now IT admins can better enforce pass codes, erase confidential data for Android and iOS devices with selective account wipe and more without users needing to install profiles. Lastly, we added IRM controls to Team Drives to prevent folks from printing, downloading or copying files they shouldn’t have access to.
Many of these protections are default-on, which means you don’t have to do a thing. Read up here, or get started using the security center for G Suite.

This one is so simple. Did you know that you can make a copy of a Google Doc or Sheet with a quick URL change? In the URL of your document, delete the information before the final backslash. In this case, change “edit” to “copy.” Done!
And since security should always be top of mind, brush up on how to manage your share settings in Docs or other apps on our Help Center.

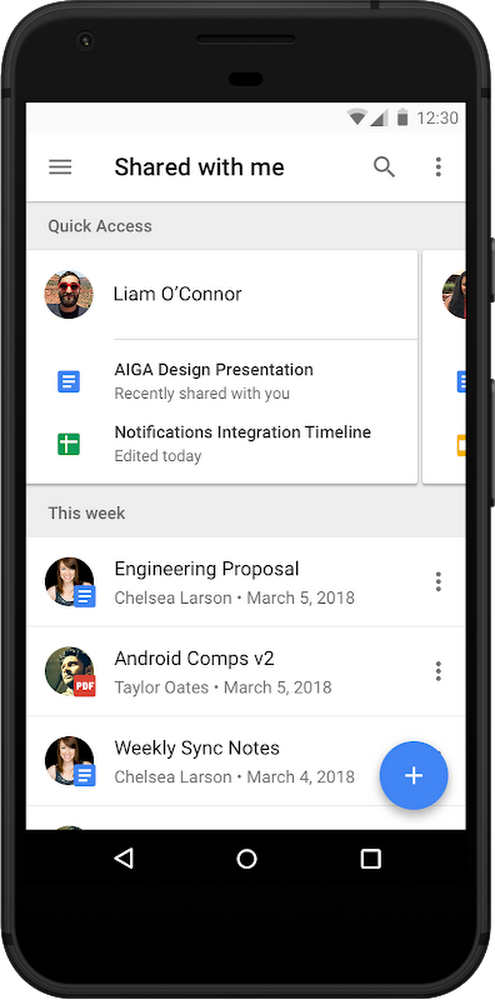
→Most of us track down files in Google Drive by searching for the name of the person who shared a file with us. Because of this, Drive is going to start intelligently organizing the “Shared with Me” section by listing names and the files that people have shared with you, so you can track down files faster.
→ Two-step verification is an easy and effective way to protect G Suite users, which is why we recommend that businesses use security keys. Moving forward, all G Suite admins—not just G Suite Business admins—will be able to manage the deployment of security keys and view usage reports. Learn more.
→ Now your jams in Jamboard will automatically save to Drive.
Here’s a full rundown of product updates in March (PDF version).
Related Articles
ICYMI in February: here’s what happened in G Suite
ICYMI in January: here’s what happened in G Suite
Subscribe to Think With Google to receive additional insights and stay on top of the latest and greatest.
